Continuous authentication
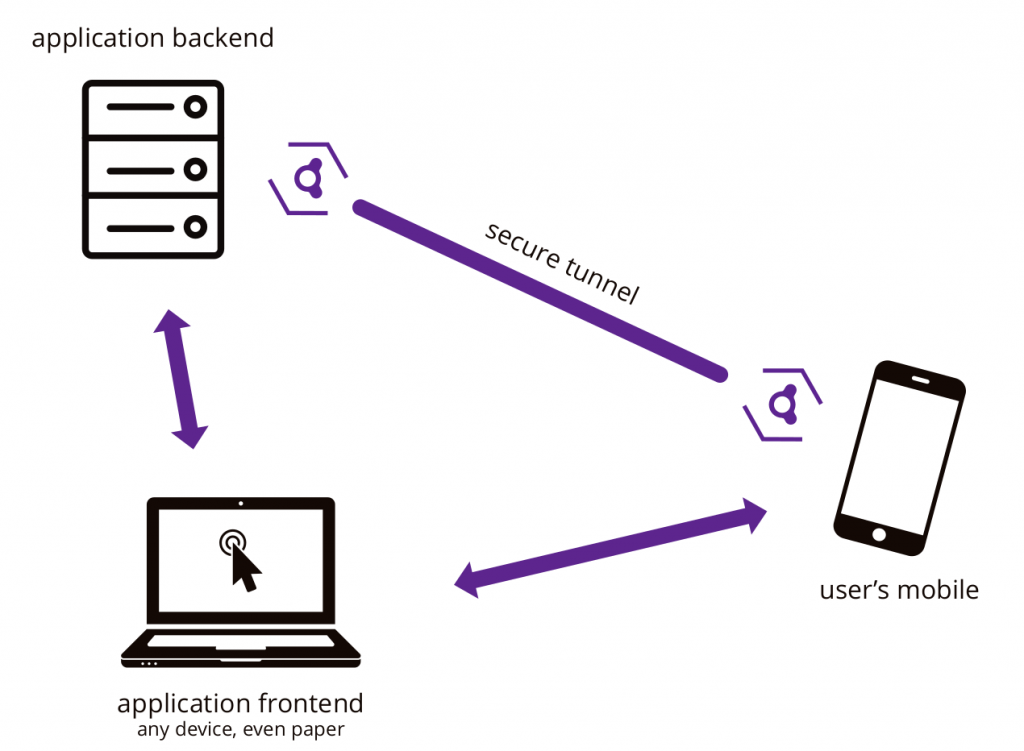
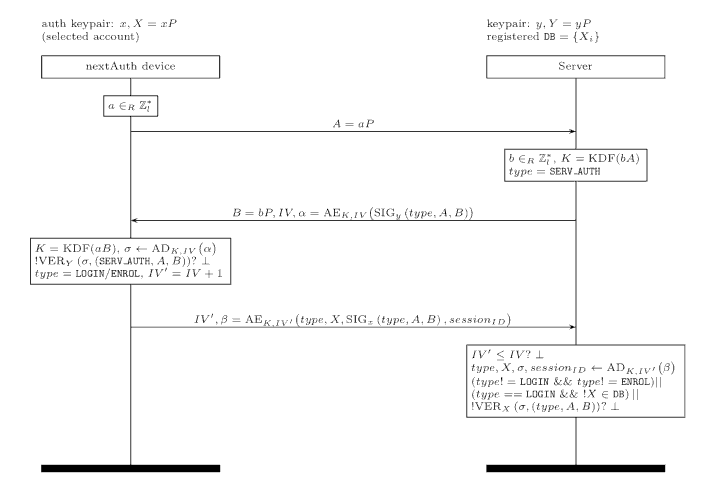
We establish a secure channel for exchanging subsequent messages between mobile and server, based on the shared key from the authentication protocol. Using this secure channel, mobile and server engage in continuous authentication. Both the server and mobile can terminate the continuous authentication process, resulting in the user being logged out.